Client Overview
US based OEM producing HVAC system including water heaters and boilers for residential/commercial buildings
Business Need
- The client was looking for a technology partner with expertise in Wi-Fi security to help them upgrade their Wi-Fi modules to meet industrial requirements
VOLANSYS Contribution
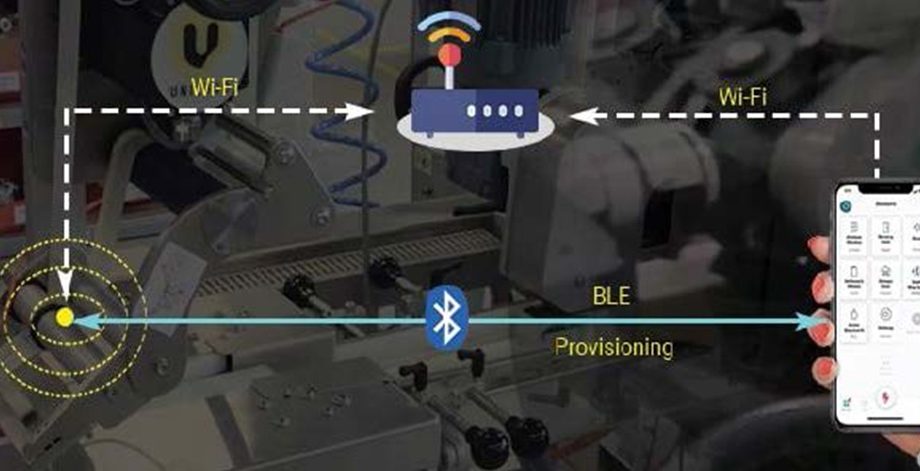
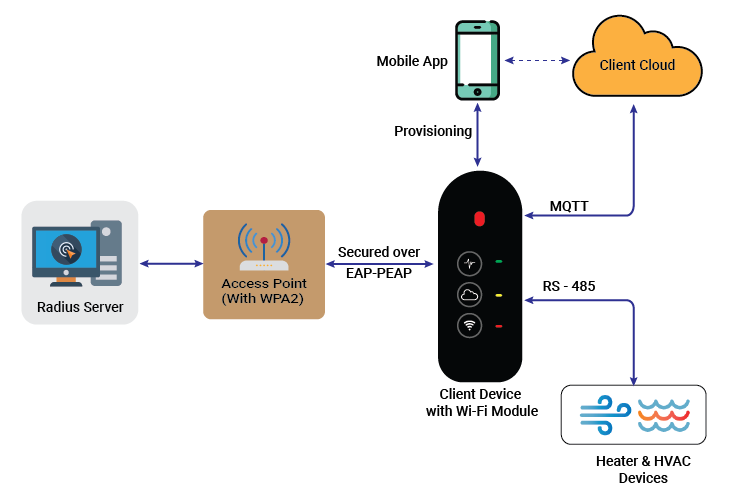
- Migrated firmware from Marvell SDK version 5.0 to latest Marvell SDK version 6.0
- Updated MQTT application with native MQTT Paho APIs
- Implemented WPA2 enterprise EAP-PEAP security with Elliptic curve crypto
- Updated device provisioning flow to share WPA2 enterprise username and password over AP mode
- Mitigated code issues making it more robust, efficient, and memory-optimized
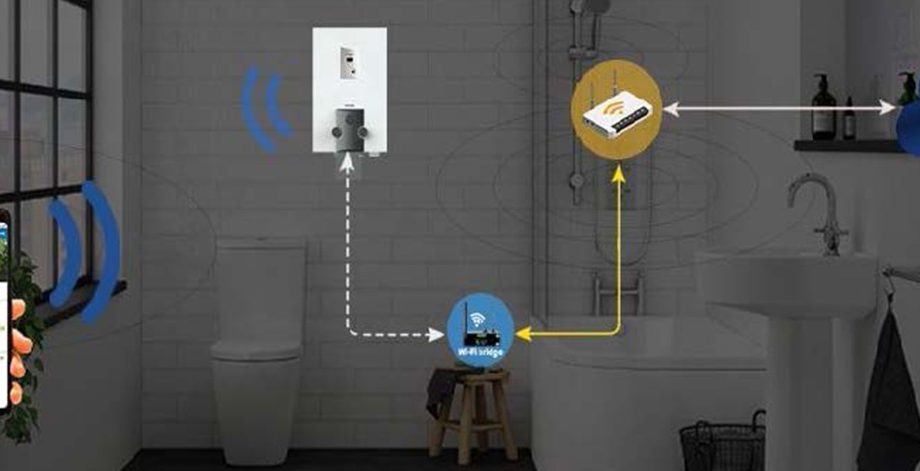
Solution Diagram
Benefits Delivered
- Enabled client to cater enterprise market with technologically upgraded and improved user security implementation for user access to cloud connected devices
EXT:- 262
Success Stories
Smart and Sustainable Air Purifier Solution to Monitor the Indoor Air Quality
Ideal Living, a US-based technology company, develops innovative solutions for health, wellness, and the home environment. The client wanted to upgrade their legacy air purifier into a smart and conne
Commercial Building Management IoT Gateway And Connected Application
A leading US based lighting and controls manufacturer delivering technical solutions for all creative lighting requirements. The client was looking for a technology partner who can enhance existing Zi
Developed Smart Stove Sensor Solution
US-based leading company providing innovative and high-quality healthcare solutions, specifically for elderly people. The client was looking for a technology partner who can design and develop Z-Wave
Thermal Sensor Application For Human Presence Detection
A global leader in the field of automation having a core-business in sensor technology. To demonstrate the capability of recently developed thermal solution in the market client was looking for a tech
HomeBridge Gateway Integration With Smart Padlocks
US based manufacturer of smart locks, providing reliability and safety for consumers and businesses. The client was looking for a technology partner to help them transform their existing padlock solut
Wireless Lighting Control Solution for Smart Farming
US-based leading manufacturer of lighting solutions for controlled environment farming/horticulture applications The client was looking for an easy-to-customize solution that can be deployed in the
Low Power Image Transfer Solution For Occupancy Sensing Solution
US-based leading semiconductor company offering innovative solutions for digital transformation. The client wanted to add a low-cost and low-power image transfer solution over BLE to its embedded comp
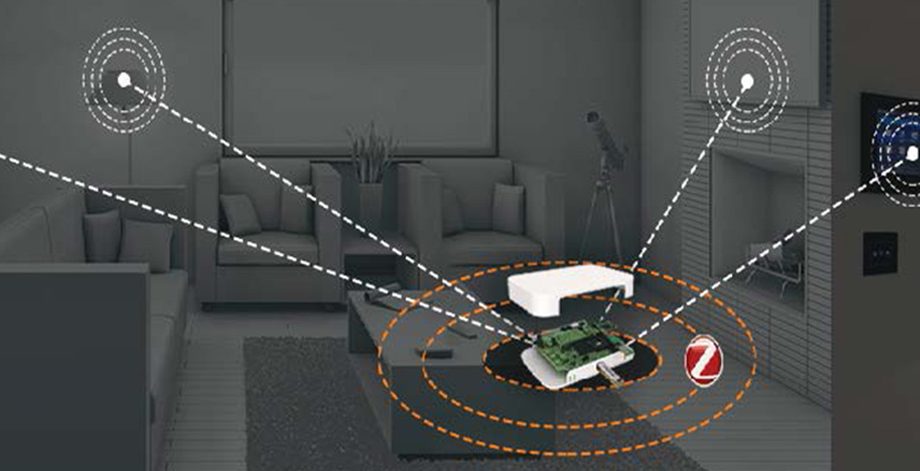
Z-Wave based Smart Solution for Home and Building
US based company in the field of energy grid providing innovative solutions of energy ecosystem & consumer smart energy devices The client wanted to build a smart solution to connect homes and bui
Connected Wheel & Fleet Management Solution
US based technology company offering solutions for transportation industry. The client was looking for an engineering partner to help them develop a cloud connected solution for fleet tire monitoring
Connected Endoscopy Device For Smart Healthcare
US-based healthcare company, Endoluxe developing innovative healthcare solutions and platforms for endoscopic procedures. The client was looking for a technology partner to design a portable and conne
Next Generation Managed Home Security Solution
US based company providing managed home security solutions for remote control and monitoring The client wanted to launch managed security and home automation solutions for their end-customers They wer
Automated Monitoring Of Labelling Solution For Fresh Farm Produces
Leading UK based Industrial labeling system provider of the farm products. The client wanted to develop stable and scalable Wi-Fi mesh solution of 50 nodes to manage and monitor labelling solution for
Smart Elderly Health Monitoring Solution
US based leading company, providing innovative and high-quality healthcare solutions, specifically for elderly people. The client was looking for a customized OEM gateway solution that can be easily i
Voice Health Monitoring Solution
US-based start-up company designing and developing innovative solutions that diagnosis the voice disorders. Being a healthcare start-up company, the client was looking for a technology partner who can
Connected Sanitary Appliances Solution
Australia based leading manufacturer of building fixtures and fittings for commercials premises. The client wanted to technologically upgrade their connected sanitary appliances solution Leveraged CEN
IoT Enabled Water Heaters/Boilers Solution Development
US based leading manufacturer of water heating, space heating, and water storage products. The client was looking for an IoT solution engineering partner to help them in building a CTA-2045 compliant
Complying High Speed Interface Connector For Cisco Certification
US-based leading provider of advanced solutions for optic and wired solutions. The client wanted an augmented support to review, fix issues and enhance the code to ensure that the product that runs on
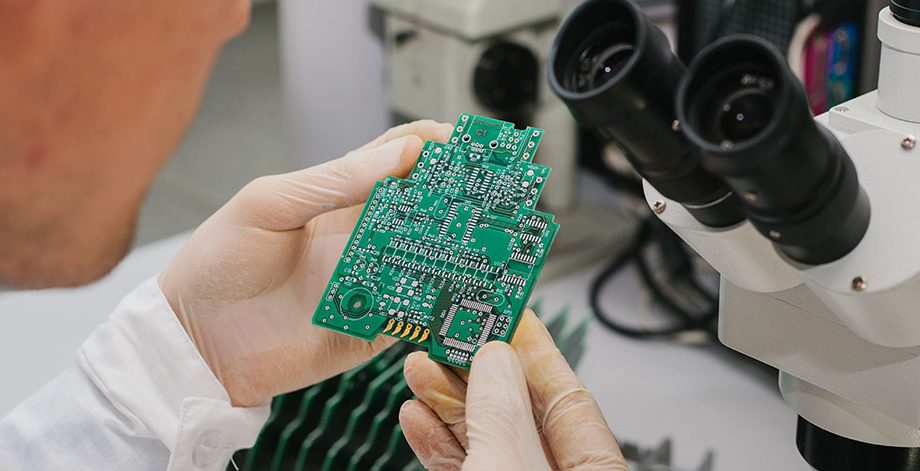
Miniaturization of Board Design with Cutting-edge Functionality
US-based engineering and manufacturing company providing embedded computing solutions through a variety of products The client wanted to expand their product portfolio with the latest NXP i.MX8M Quad-
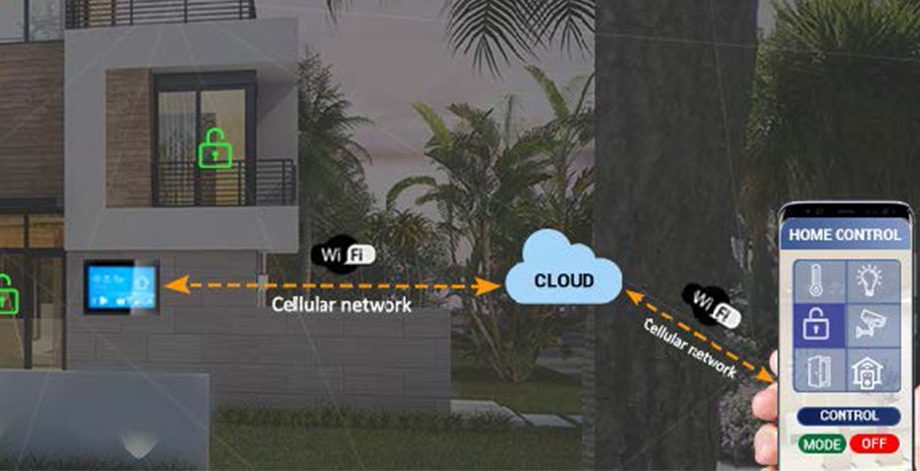
Enhanced Enterprise Network Security For Cloud Connected Devices
US based OEM producing HVAC system including water heaters and boilers for residential/commercial buildings The client was looking for a technology partner with expertise in Wi-Fi security to help the
FDA Compliant Automated External Defibrillator Development
US based technology company delivering innovative healthcare solutions with better care at lower cost. The client required a technology partner to develop a neurostimulation wearable device that allow
Micro Infusion Pump With Automated Operations
US based healthcare company providing innovative medical devices and solutions for patient care. The client was looking for a development partner with expertise in healthcare domain to develop control
Zigbee Integration With Home Automation Gateway
US based home automation company providing smart apartment solution The client was looking for a proven partner in enabling IoT connectivity to expand their current Z-Wave based Home Automation Soluti
SPI Flash Performance Evaluation Board
US based technology company designing & developing high performance integrated circuits, flash & memory products. With recently launched new flash products, the client wanted to create a sales
Smart Low-Cost Eye Diagnostic System
US-based start-up company developing smart eye diagnostic solution to replace traditional eye care instrument. The client wanted to build a low-cost smart eye diagnostic solution that captures corneal
Next- Generation Network Security Device
US-based company providing highly secured next-generation smart network security solutions, specializing in access and extraction. The client’s existing network security solution was based on i.MX6
Pre-Sales And Post-Sales Technical Support
US based leading semiconductor manufacturer offering microcontrollers and processors to sensors, analog ICs and connectivity. With a major business acquisition along with a large customer base, the cl
Retrofit Solution For Fault Detection In Power Lines
German fortune 500 company, a leader in developing large energy utility solutions like turbines, transmission, & power distribution. The client’s existing solution for fault detection has a larg
Multiple BLE Chipsets Support For Occupancy Sensing Solution
US-based leading semiconductor company offering innovative solutions for the digital transformation. The client wanted to enhance its existing occupancy sensing solution by adding the support of a SiL
Smart Wireless HVAC Zoning System
US based leading manufacturer of HVAC zoning dampers and zoning systems The client wanted to transform legacy wired HVAC zoning system into smart wireless zoning system and enable remote access to get
Wi-Fi Enabled Automotive Rear-Vision System
US based company developing electronic products for automotive and aerospace industries. The client wanted to enhance performance of Wi-Fi enabled solution for automobile display/rare view mirror to i
Smart Home Security Control Panel With Connected App
A global leader in smart connected devices & systems for residential, security, access control, AV distribution, and digital health markets. To maintain the existence in the competitive market of
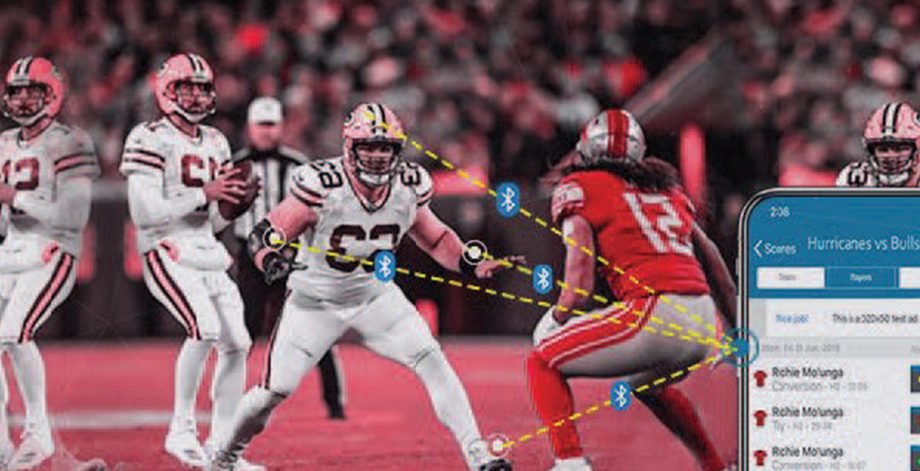
On-Field Sports-Tech Gadget For Players
US-based company with a focus on advanced sports-tech gadgets manufacturing The client wanted to deliver a differentiating sports-tech gadget in the market for advanced monitoring and analyzing data t
Development Of Universal Communication Module (UCM)
US-based manufacturer of HVAC system and water heaters for residential/commercial buildings. The client wanted to upgrade their existing solutions to communicate with the smart grid over an establishe
Connected Elevator Solution Development
US-based IoT enabled elevator solution provider for homes and industries. The client wanted to design a cost-effective IoT solution that would connect any elevator to the cloud to collect the elevator
Automatic Testing Equipment Development
US-based leading innovator building high energy ignition and flame detection technology solutions. The client wanted to develop an automated testing tool that can help them to maintain the consistency
Connected Elevator Solution Development
US-based IoT enabled elevator solution provider for homes and industries. The client wanted to design a cost-effective IoT solution that would connect any elevator to the cloud to collect the elevator
Aircraft Structure Health Monitoring Solution
US based company providing structural health monitoring for aircrafts, bridges, machinery and more. The client wanted to stabilize their existing solution to real-time monitor the structure health of
Aircraft Wireless Cabin Control System (WCCS) Development
UK based company providing advanced, technology-led defense, aerospace, and security solutions. The client wanted to develop a wireless cabin control system to reduce overall weight of the aircraft an
Cloud Connected Smart Safe/Locker
US based fortune 500 company in connected home and security products. The client was looking for an expert in connected product engineering to help them design a BLE and Wi-Fi enabled smart safe opera
Developing Next-Gen Fire Safety Door Devices For Smart Homes
US based company offering lifesaving smart devices for the event of fire. The client wanted to launch their new-age fire safety devices pre-integrated with leading smart home hubs available in the mar
Wireless Charging Solution For Electric Automobiles
US-based leading company, developing innovative wireless charging solutions for electric automobiles. The client was planning to launch a next-generation wireless charging product in the area of Autom
Modernization Of Stock Management Process Using Technology
A fortune 500 company having chain of fast-food restaurants across the globe. The client wanted to improve their food inventory management system. For the same, they wanted to develop a connected solu
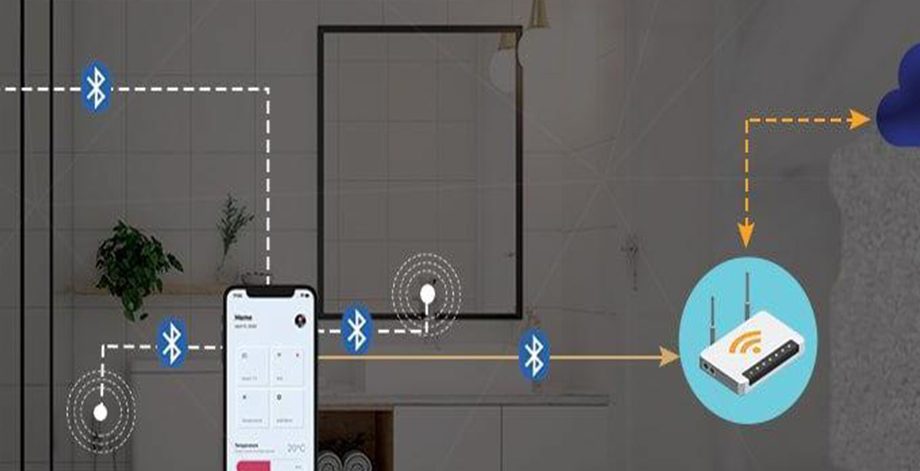
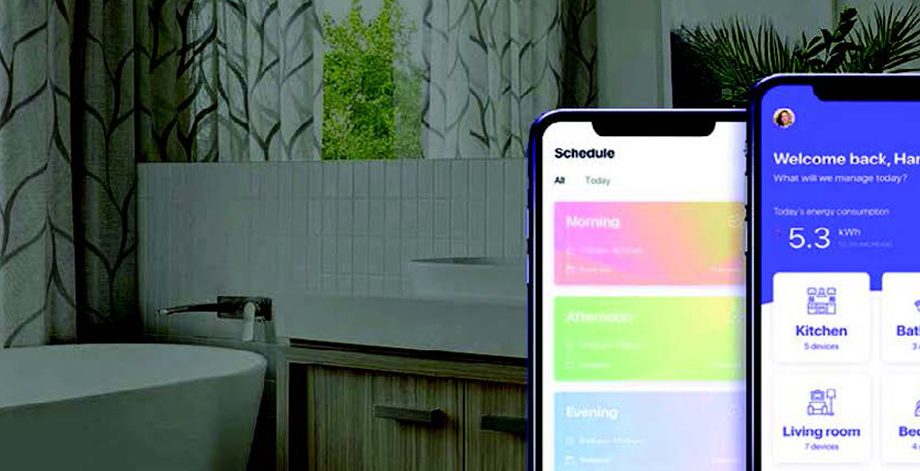
Personalized Bathing Experience With Connected Bathroom
North America based supplier and manufacturer of bathroom accessories. To increase the market share, the client wanted to expand the business by providing connected accessories as well as an overall b
Battery Operated Smart Smoke Sensing Device
US based fortune 500 company in connected home and security products. The client was looking for a partner having expertise in Z-Wave to help them in upgrading their Z-Wave device They were looking fo
Connected Fire Safety Solution
US based fortune 500 company in connected home and security products The client was looking for a technology partner who has expertise in providing end-to-end IoT solutions to help them develop and sc
Hassle-Free Fresh Food Access From Connected Freezer
US-based leading retail chain providing nutritionally advised and fresh-frozen food items. The client wanted to convert their legacy freezer to a smart and connected one where the inventory stocks pre
Platform To Evaluate Environmental Sensor Capabilities
Global manufacturer of advance electronic devices/components in the field of automation. The client was looking for a technology partner to enable integration of their environmental sensors with th
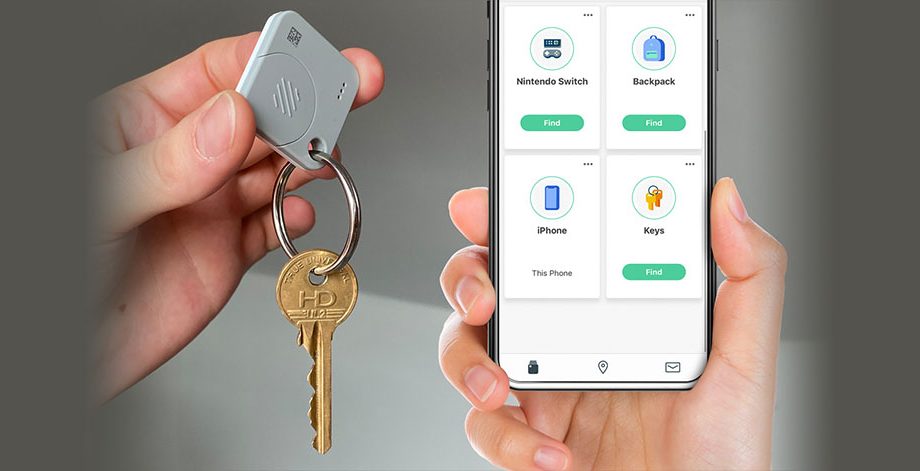
Handheld Tracking Device For Personal Belongings
A product manufacturing company deriving solutions with precise engineering to improve people’s lives. The client wanted to design a tracking device that can prevent and protect personal belongings
Automated Radio Channel Assessment Controller [RCAC]
A US based IT Solution Provider. The client was looking for an engineering partner who could help them develop a multi-radio, multi-frequency wireless connectivity device prototype for automated tunin
Dosage Infusion Pump Firmware Development & Quality Engineering
A US based leading pharmaceutical company. The client wanted to develop a FDA compliance medical Infusion pump device to automate and control desired medical dosage flow rate, ensure accuracy in the a
Interactive Digital Display Content Management And Delivery Solution
US based manufacturer with more than 500k touchscreen displays, monitors, POS devices in field . The client wanted to develop an end-to-end SaaS Solution for remote interactive display management a
WAN Gateway For Safeguarding Connected Devices And Networks
US-based network security company providing software-defined cybersecurity solutions for data centers. Being a leader in the cyber security industry, the client wanted to design a small form factor of
Wireless Connectivity Device Development
A US based Wireless Networking Solution Provider. The client wanted to develop an 802.11 A/B/G/N based device with support for 6 radio cards and connect up-to 744[6 * 124] wireless 802.11N end-connect